DNS Leaks, Fingerprints, and Other Windows Privacy Checks People Skip
From Browser Fingerprints to DNS Leaks: The Privacy Checks PC Users Ignore
Stop confusing visible settings with actual privacy state
Most users stop at the visible settings because the invisible ones are annoying, and that is exactly where the leaks keep hiding. That is why this section matters. In browser exposure, troubleshooting, and noisy web habits, stop confusing visible settings with actual privacy state is less about theory and more about how people behave when the connection looks good enough and the task feels urgent. For people who think they already hardened their browser and probably stopped halfway, the weak spot is usually repetition rather than drama. A stale profile. A trusted hotspot that should not be trusted. A session reused because reopening it feels annoying. I think that is why generic privacy advice keeps sounding smarter than it is useful. It assumes stable context, clean attention, and users who always notice drift before it matters. Real life is messier. A Windows setup only earns trust when it still works on rushed days, on tired days, and on days when the network conditions shift halfway through the job. So the standard here is not perfection. It is durable behavior under normal pressure.
Which fingerprinting vectors survive casual hardening
A lot of people assume this part is already handled, then discover later that they were only looking at the surface. In browser exposure, troubleshooting, and noisy web habits, which fingerprinting vectors survive casual hardening interacts with background state that most users never inspect closely enough: resolver changes, saved tokens, extension chatter, cached sessions, and browser residue that keeps old assumptions alive. Nothing has to look broken for leakage to grow. That is the trap, really. Most sessions still finish, so confidence goes up while observability quietly gets better for everyone except the user. The useful move is verification before trust. Check the route. Check the active identity context. Check whether the machine is carrying assumptions from an earlier session that should have been reset already. Maybe that sounds repetitive. Good. Repetition is usually what stops drift from becoming the default. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one.
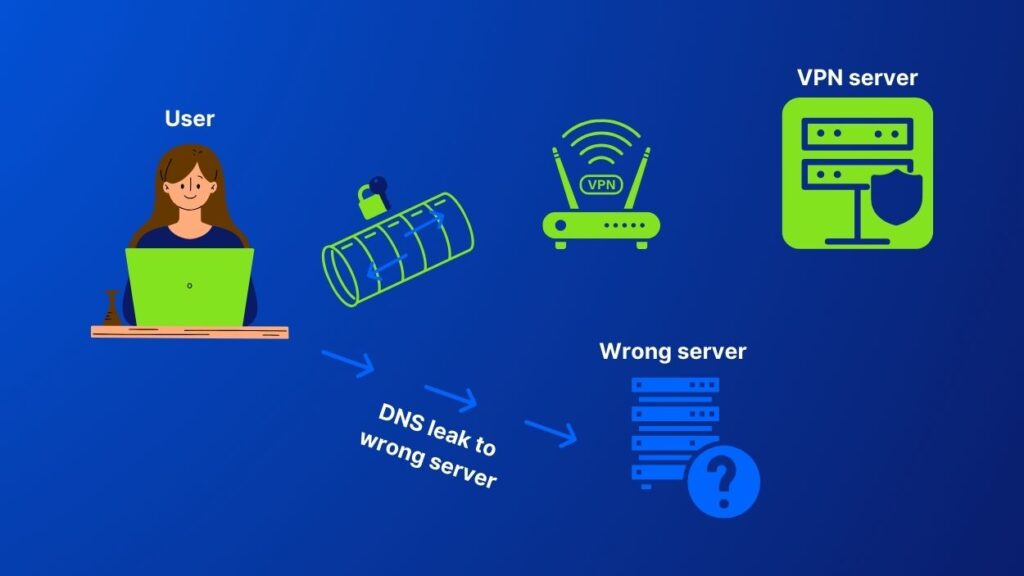
How resolver behavior quietly undermines confidence
Shortcut thinking usually shows up here. How resolver behavior quietly undermines confidence is not solved by one shiny control, even though people understandably want that answer. A VPN helps in its own lane, sometimes quite a bit, but it does not repair weak endpoint hygiene, sloppy account boundaries, or browser habits that keep reintroducing context leakage. The better rule is pretty blunt: decide when protected routing is mandatory, decide what happens when it fails, and keep the rest of the stack disciplined enough that the tunnel is not wasted by sloppy follow-through. Less marketable, sure. Closer to reality too. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one. Boring, honestly. Boring also survives real work. Small discipline beats dramatic promises every single time. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. That sounds fussy. It is still cheaper than guessing later.
Tighten Windows and browser layers in the right order
Most users stop at the visible settings because the invisible ones are annoying, and that is exactly where the leaks keep hiding. That is why this section matters. In browser exposure, troubleshooting, and noisy web habits, tighten windows and browser layers in the right order is less about theory and more about how people behave when the connection looks good enough and the task feels urgent. For people who think they already hardened their browser and probably stopped halfway, the weak spot is usually repetition rather than drama. A stale profile. A trusted hotspot that should not be trusted. A session reused because reopening it feels annoying. I think that is why generic privacy advice keeps sounding smarter than it is useful. It assumes stable context, clean attention, and users who always notice drift before it matters. Real life is messier. A Windows setup only earns trust when it still works on rushed days, on tired days, and on days when the network conditions shift halfway through the job. So the standard here is not perfection. It is durable behavior under normal pressure.
Controls worth fixing before marginal tweaks
A lot of people assume this part is already handled, then discover later that they were only looking at the surface. In browser exposure, troubleshooting, and noisy web habits, controls worth fixing before marginal tweaks interacts with background state that most users never inspect closely enough: resolver changes, saved tokens, extension chatter, cached sessions, and browser residue that keeps old assumptions alive. Nothing has to look broken for leakage to grow. That is the trap, really. Most sessions still finish, so confidence goes up while observability quietly gets better for everyone except the user. The useful move is verification before trust. Check the route. Check the active identity context. Check whether the machine is carrying assumptions from an earlier session that should have been reset already. Maybe that sounds repetitive. Good. Repetition is usually what stops drift from becoming the default. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one.
How updates reopen leaks when settings start conflicting
Shortcut thinking usually shows up here. How updates reopen leaks when settings start conflicting is not solved by one shiny control, even though people understandably want that answer. A VPN helps in its own lane, sometimes quite a bit, but it does not repair weak endpoint hygiene, sloppy account boundaries, or browser habits that keep reintroducing context leakage. The better rule is pretty blunt: decide when protected routing is mandatory, decide what happens when it fails, and keep the rest of the stack disciplined enough that the tunnel is not wasted by sloppy follow-through. Less marketable, sure. Closer to reality too. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one. Boring, honestly. Boring also survives real work. Small discipline beats dramatic promises every single time. That sounds fussy. It is still cheaper than guessing later. People skip this because it feels small, then pay for that laziness afterward.
Use VPN as one layer in a leak-focused stack
Most users stop at the visible settings because the invisible ones are annoying, and that is exactly where the leaks keep hiding. That is why this section matters. In browser exposure, troubleshooting, and noisy web habits, use vpn as one layer in a leak-focused stack is less about theory and more about how people behave when the connection looks good enough and the task feels urgent. For people who think they already hardened their browser and probably stopped halfway, the weak spot is usually repetition rather than drama. A stale profile. A trusted hotspot that should not be trusted. A session reused because reopening it feels annoying. I think that is why generic privacy advice keeps sounding smarter than it is useful. It assumes stable context, clean attention, and users who always notice drift before it matters. Real life is messier. A Windows setup only earns trust when it still works on rushed days, on tired days, and on days when the network conditions shift halfway through the job. So the standard here is not perfection. It is durable behavior under normal pressure.
When routed sessions reduce network-level observability
A lot of people assume this part is already handled, then discover later that they were only looking at the surface. In browser exposure, troubleshooting, and noisy web habits, when routed sessions reduce network-level observability interacts with background state that most users never inspect closely enough: resolver changes, saved tokens, extension chatter, cached sessions, and browser residue that keeps old assumptions alive. Nothing has to look broken for leakage to grow. That is the trap, really. Most sessions still finish, so confidence goes up while observability quietly gets better for everyone except the user. The useful move is verification before trust. Check the route. Check the active identity context. Check whether the machine is carrying assumptions from an earlier session that should have been reset already. Maybe that sounds repetitive. Good. Repetition is usually what stops drift from becoming the default. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one.
What the tunnel cannot hide from sloppy behavior
Shortcut thinking usually shows up here. What the tunnel cannot hide from sloppy behavior is not solved by one shiny control, even though people understandably want that answer. A VPN helps in its own lane, sometimes quite a bit, but it does not repair weak endpoint hygiene, sloppy account boundaries, or browser habits that keep reintroducing context leakage. In the higher-risk cases, Windows VPN is a practical way to force encrypted routing without inventing a workaround in the middle of the session. The better rule is pretty blunt: decide when protected routing is mandatory, decide what happens when it fails, and keep the rest of the stack disciplined enough that the tunnel is not wasted by sloppy follow-through. Less marketable, sure. Closer to reality too. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one. That sounds fussy. It is still cheaper than guessing later.
Verify often enough that drift never becomes invisible
Most users stop at the visible settings because the invisible ones are annoying, and that is exactly where the leaks keep hiding. That is why this section matters. In browser exposure, troubleshooting, and noisy web habits, verify often enough that drift never becomes invisible is less about theory and more about how people behave when the connection looks good enough and the task feels urgent. For people who think they already hardened their browser and probably stopped halfway, the weak spot is usually repetition rather than drama. A stale profile. A trusted hotspot that should not be trusted. A session reused because reopening it feels annoying. I think that is why generic privacy advice keeps sounding smarter than it is useful. It assumes stable context, clean attention, and users who always notice drift before it matters. Real life is messier. A Windows setup only earns trust when it still works on rushed days, on tired days, and on days when the network conditions shift halfway through the job. So the standard here is not perfection. It is durable behavior under normal pressure.
Checks for route, DNS, and profile hygiene
A lot of people assume this part is already handled, then discover later that they were only looking at the surface. In browser exposure, troubleshooting, and noisy web habits, checks for route, dns, and profile hygiene interacts with background state that most users never inspect closely enough: resolver changes, saved tokens, extension chatter, cached sessions, and browser residue that keeps old assumptions alive. Nothing has to look broken for leakage to grow. That is the trap, really. Most sessions still finish, so confidence goes up while observability quietly gets better for everyone except the user. The useful move is verification before trust. Check the route. Check the active identity context. Check whether the machine is carrying assumptions from an earlier session that should have been reset already. Maybe that sounds repetitive. Good. Repetition is usually what stops drift from becoming the default. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one.
When a reset beats one more careful patch
Shortcut thinking usually shows up here. When a reset beats one more careful patch is not solved by one shiny control, even though people understandably want that answer. A VPN helps in its own lane, sometimes quite a bit, but it does not repair weak endpoint hygiene, sloppy account boundaries, or browser habits that keep reintroducing context leakage. The better rule is pretty blunt: decide when protected routing is mandatory, decide what happens when it fails, and keep the rest of the stack disciplined enough that the tunnel is not wasted by sloppy follow-through. Less marketable, sure. Closer to reality too. That sounds obvious, but obvious controls are the ones people skip first when the day gets noisy. The whole point is to make the safe path easier than the improvised one. Boring, honestly. Boring also survives real work. Small discipline beats dramatic promises every single time. That sounds fussy. It is still cheaper than guessing later. People skip this because it feels small, then pay for that laziness afterward.